Migrating an AWS member account from AWS Organizations to AWS Control Tower can be a game-changer for your cloud governance strategy. It offers a comprehensive framework that combines the capabilities of various AWS services, including AWS Organizations, to streamline your account governance and ensure consistent compliance across your multi-account environment.
In this article, we will delve into the process of migrating an existing AWS account to AWS Control Tower, highlighting the benefits, prerequisites, limitations, and step-by-step instructions to successfully complete the migration.
Why Migrate to AWS Control Tower?
AWS Control Tower presents a wide array of advantages for organizations seeking enhanced governance and compliance in their AWS environment. By enrolling your member account in it, you gain access to preventive and detective guardrails, which enable you to enforce security best practices and detect policy violations effectively. Additionally, it simplifies the management of multiple AWS accounts by providing a centralized platform for account governance, ensuring consistent policies and configurations across your organization.
Before initiating the migration process, consider the following prerequisites and limitations.
Prerequisites:
- An active AWS account: Ensure that you have an active AWS account to proceed with the migration process.
- Setup: Set up AWS Control Tower in your target organization within AWS Organizations. Follow the instructions provided in the AWS Control Tower documentation https://docs.aws.amazon.com/controltower/latest/userguide/setting-up.html for the setup process.
- Administrator credentials: Obtain administrator credentials for AWS Control Tower, as you need to be a member of the “AWSControlTowerAdmins” group to perform the migration.
- Administrator credentials for the source AWS account: Ensure that you have administrator-level credentials for the source AWS account that you intend to migrate to.
Limitations:
- Different management accounts: The source management account in AWS Organizations must be different from the target management account in AWS Control Tower.
- Version: Make sure you are using AWS Control Tower version 2.3 (February 2020) or later. Refer to the ‘release notes’ for more details on the latest version.
Now that we have the prerequisites and limitations covered, let’s dive into the architecture and migration process.
Architecture
The migration process follows a well-defined pattern, ensuring a seamless transition for your member account. Find the high-level architecture below.
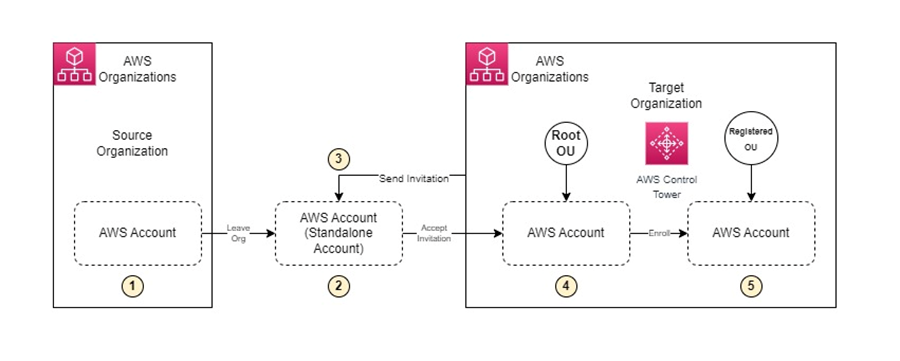
Steps Involved in the Migration
- Leaving the source organization in AWS Organizations: The member account leaves the source organization in AWS Organizations, becoming a standalone account managed independently by account administrators.
- Invitation to join the target organization: The target organization, governed by AWS Control Tower, sends an invitation to the member account to join the organization.
- Accepting the invitation: The standalone account accepts the invitation and becomes a member of the target organization.
- Enrollment: The account is enrolled in AWS Control Tower and moved to a registered organizational unit (OU) within the target organization. At this point, all enabled guardrails defined in the registered OU take effect.
With the architectural overview in mind, let’s delve into each step of the migration process, starting with verifying the member account’s ability to operate as a standalone account.
Verify Standalone Account Capability
Before removing the member account from the source organization, you need to ensure that it has all the necessary information to function as a standalone account. While AWS Organizations console, API, or CLI commands might not automatically collect the required information for standalone accounts, you can manually add it by signing in and specifying a payment method, support plan, and contact information.
Visit the ‘Before removing an account from the organization’ section in the AWS Organizations documentation for detailed guidance on the prerequisites for standalone accounts.
Remove the Member Account from the Source Organization
To initiate the migration process, you must remove the member account from its source organization in AWS Organizations. Depending on your access level, you can either sign in to the organization’s management account and remove the member account or sign in to the member account and leave the organization. If you lack administrator-level credentials, seek assistance from your organization’s administrator.
When leaving the organization, ensure that the member account has the necessary support plan, contact information, and payment information. Keep in mind that once the account leaves the organization, it becomes a standalone account and incurs charges according to the provided payment and billing information.
Verification of Account Exit from Source Organization
After removing the member account from the source organization, verify that it is no longer part of the organization by checking the AWS Organizations console. The “Leave organization” button should no longer be visible, and any pending invitations from other organizations should appear instead.
Remove IAM Roles from the Source Organization
When a member account leaves an organization, the IAM roles created by AWS Organizations or administrators are not automatically deleted. To terminate access from the source organization’s management account, manually delete these IAM roles. Refer to the Deleting roles or instance profiles section in the IAM documentation for detailed instructions on removing IAM roles.
Sign In
To proceed with the migration, sign in to the AWS Control Tower console using administrative credentials. It is essential to note that you should not use the root user (management account) credentials for enrolling an AWS Organizations account into AWS Control Tower, as it may result in an error message.
Invite the Member Account to Join the Target Organization
Once signed in to the AWS Organizations console, navigate to the “AWS Accounts” page to initiate the invitation process. Choose the “Add an AWS account” option and select “Invite an existing AWS account.” Provide the necessary account information, including the 12-digit account number, account description, and tags, and then send the invitation. It is crucial to ensure that the account transfer does not impact any applications or network connectivity.
Test Applications and Connectivity
After the member account receives the invitation and accepts it, it becomes visible on the “AWS Accounts” page of the console. However, it is essential to conduct thorough testing to ensure that applications associated with the account run smoothly and that connectivity, such as VPN or AWS Direct Connect, remains unaffected by the migration process.
Review and Fix Guardrail Violations
AWS Control Tower comes with a set of mandatory, preventive guardrails enabled by default during the landing zone setup. Before proceeding with the account enrollment, review these guardrails and fix any violations to ensure compliance. Preventive guardrails play a crucial role in maintaining the account’s compliance and preventing policy violations. While violations of preventive guardrails may affect enrollment, detective guardrail violations, if detected after successful enrollment, appear in the dashboard without impacting the enrollment process. Here’s the documentation for detailed information on guardrails in AWS Control Tower.
Check Connectivity after Fixing Guardrail Violations
In some cases, fixing guardrail violations may require closing specific ports or disabling services. Before enrolling the account, ensure that applications relying on these ports and services are remediated. Conduct thorough checks to verify network connectivity and confirm that applications and dependencies remain unaffected by the account transfer.
Enroll the Account in AWS Control Tower
To enroll the member account into AWS Control Tower, access the “Account Factory” page within the AWS Control Tower console and select “Enroll account.” Fill in the necessary details, including the account email address, display name, IAM Identity Center email address, account owner’s first and last name, and the OU in which you want to enroll the account. It is crucial to ensure that all the applied AWS Config rules and configurations align with the desired governance policies. Follow the instructions provided in the Enroll an existing account section of the AWS Control Tower documentation for a smooth enrollment process.
Verify the Enrolled Account
After enrolling the member account, navigate to the “Accounts” section in AWS Control Tower and verify that the account’s state changes from “Enrolling” to “Enrolled.” This transition indicates successful enrollment, and the account is now governed by AWS Control Tower. Monitor the AWS Control Tower dashboard for any guardrail violations and take appropriate actions to rectify them. Remember that guardrails defined within the registered OU automatically apply to the enrolled member account.
Troubleshooting Common Issues
While the migration process is designed to be smooth, you may encounter some issues along the way. Here are a couple of common issues and their resolutions:
Issue: An unknown error occurred. Try again later or contact AWS Support.
This error message typically occurs when root user credentials (management account) are used to enroll a new account in AWS Control Tower. To resolve this issue, use non-root, full-access user credentials with administrative permissions. Refer to the AWS IAM Identity Center documentation for guidance on assigning administrative access to users.
Issue: The AWS Control Tower Activities page displays a Get Catastrophic Drift action.
This action reflects a drift check of the service and does not indicate any issues with the AWS Control Tower setup. No further action is required for this message.
Conclusion
Migrating an AWS member account from AWS Organizations to AWS Control Tower can significantly simplify your cloud governance and enhance compliance across your organization. By following the step-by-step process outlined in this article, you can seamlessly migrate your account, leverage the power of preventive and detective guardrails, and ensure consistent governance in your AWS environment.
Remember to regularly monitor the dashboard for guardrail violations and promptly address any compliance issues. By adhering to best practices and leveraging the features provided, you can optimize your cloud operations and mitigate potential risks.