AWS Network Firewall is a managed network service provided by AWS, which was launched in November 2020 in the US East (N. Virginia), the US West (Oregon), and Europe (Ireland). This cloud-native solution helps organizations to filter and inspect the network traffic to and from VPC’s. A solid alternative to the third-party firewall solutions, it has been implemented by several customers as it integrates easily with all the AWS resources. In 2021 AWS firewall achieved some major milestones like PCI-DSS, ISO Compliance, etc. This further led to its growing traction across regions, such as Asia Pacific (Mumbai, Singapore, and Sydney), and EU (London).
Since AWS Network Firewall is a cloud-native solution, organizations get AWS support whenever required. It also helps expedite the implementation of the infrastructure. On the other hand, using a third-party firewall is time-intensive when it comes to learn and implement it with a trial & error approach.
Key Components of AWS Network Firewall
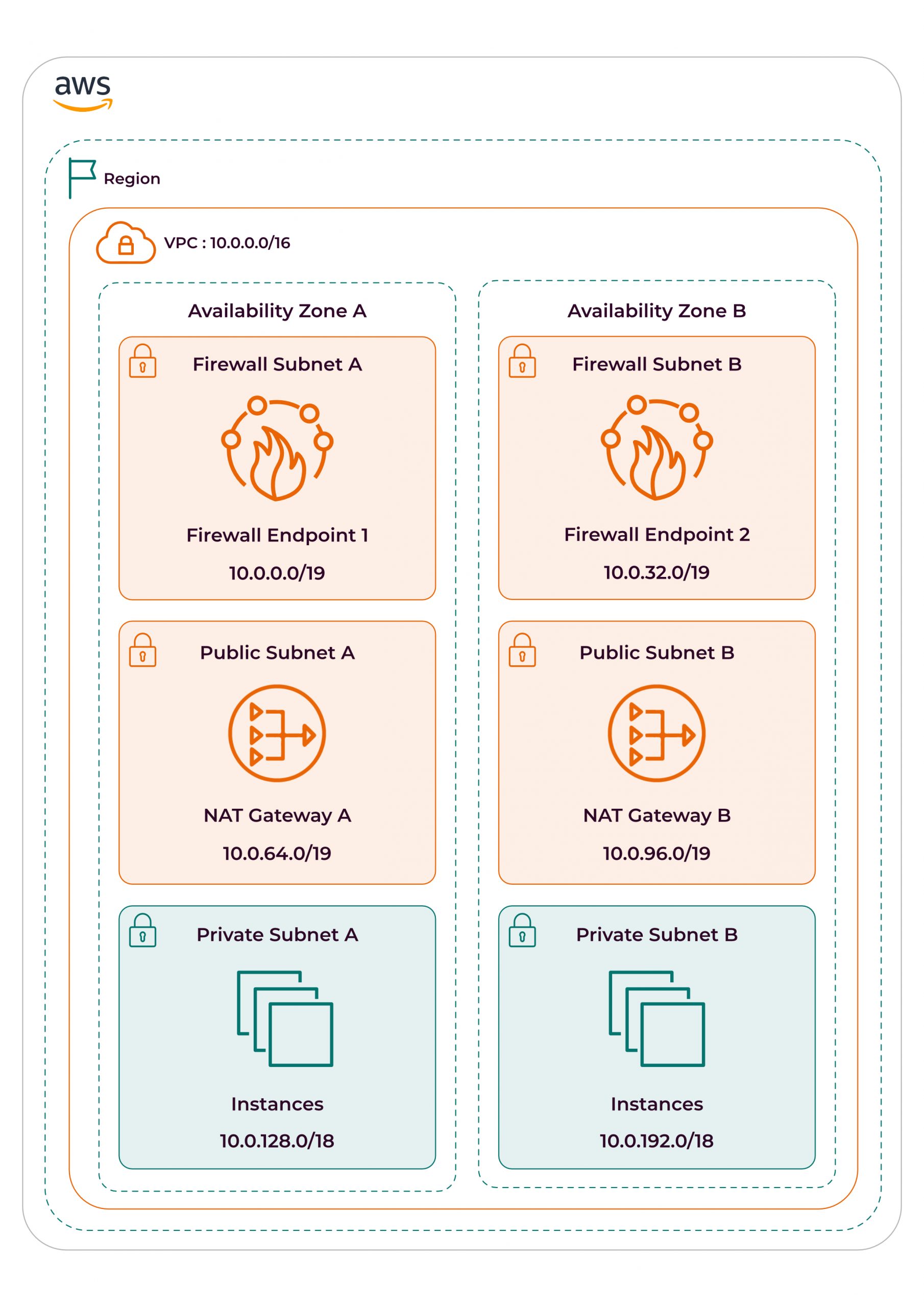
An AWS Network Firewall can be created under the VPC service from the console. At the time of firewall creation, organizations have to provide the subnets of all the AZ’s in which they look to deploy the firewall endpoint. Creating separate subnets for firewall endpoints is recommended, specifically in each AZ. Every AWS Network Firewall is associated with a Firewall Policy, which is a group of rules. Under the firewall policy, the stateless and stateful rules can be defined based on the network requirements.
AWS Network Firewall – Deployment Models
Depending on the infrastructure, AWS recommends three deployment models depending on the use case and requirement.
Distributed Firewall Model
This model is suitable for North-South (VPC to the Internet) traffic flow, which means all the traffic for public resources can be monitored and filtered by this model. The misconfiguration and radius blast are the lowest and the cost applies per AWS Network Firewall endpoint.
In distributed firewall, as shown in the above example, a firewall subnet is created for each AZ. Here, the firewall endpoints are launched. It is best practice to create a separate firewall endpoint for each AZ so that the traffic for that particular AZ will flow only through its respective endpoint.
Centralized Firewall Model
The centralized firewall is ideal for following traffic flows:
- East-West: VPC to VPC traffic flow
- North-South: VPC to Internet traffic flow
- North-South: VPC to on-prem via VPN or DX traffic flow
The misconfiguration and radius blast is medium while the cost applies as per AWS Transit Gateway attachments, AWS Network Firewall endpoints, and AWS Transit Gateway data being processed.
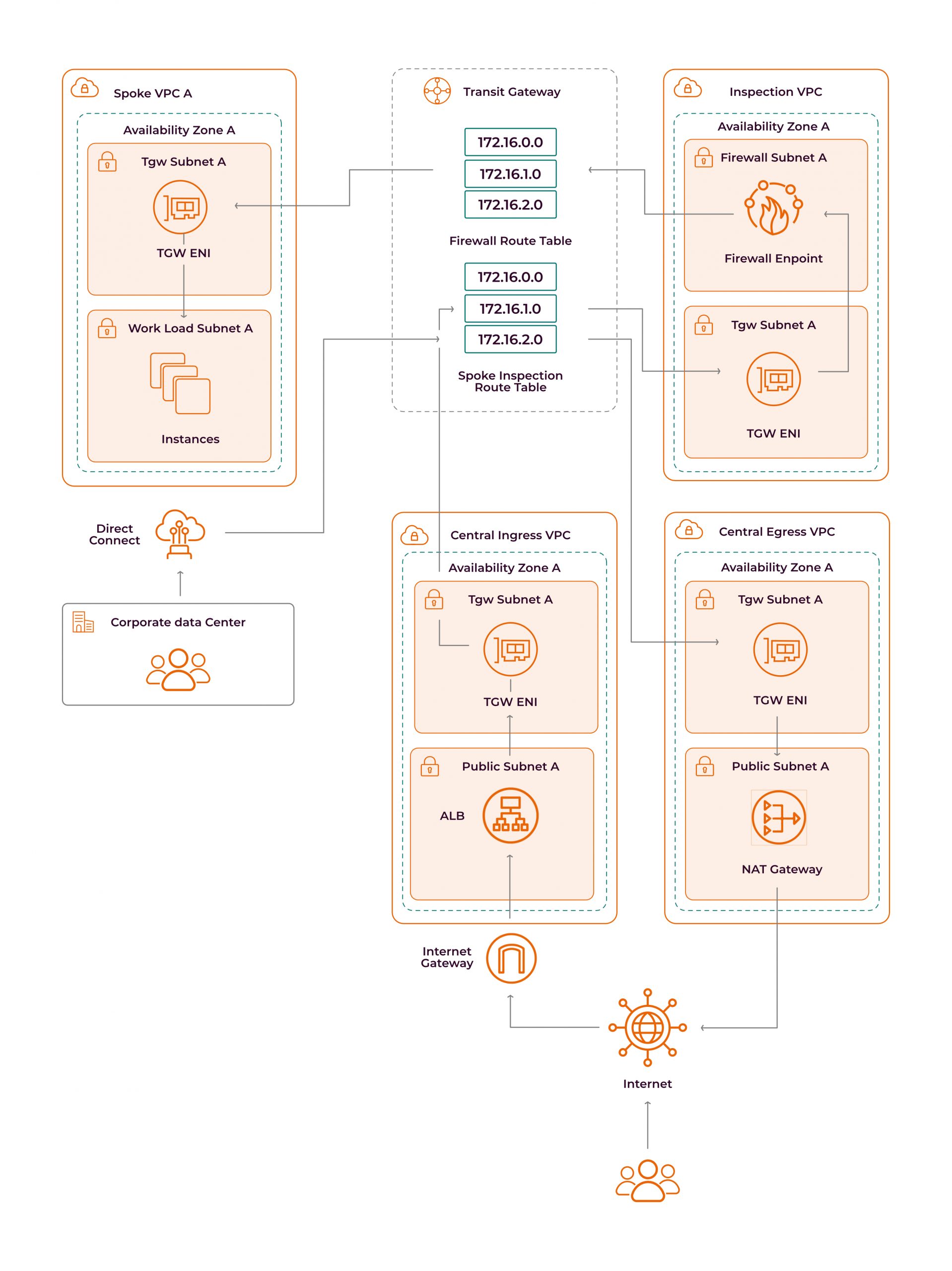
In a centralized firewall, we create 3 separate VPCs, where each takes care of a different traffic flow.
- Inspection VPC: VPC to VPC and VPC to on-premises (East-West and North-South).
- Central Egress VPC: VPC to only outbound internet traffic flow (North-South) with NAT Gateway.
- Central Ingress VPC: VPC to outbound and inbound internet traffic flow (North-South) with IGW.
All traffic flows through the transit gateway and hence, transit gateway attachments need to be created for each VPC. To ensure flow symmetry, the appliance mode of transit gateway attachment must be enabled for all three firewall VPCs.
The appliance mode can only be enabled by AWS CLI –
aws ec2 create-transit-gateway-vpc-attachment --transit-gateway-id tgw-0262a0e521EXAMPLE --vpc-id vpc-07e8ffd50f49335df --subnet-id subnet-0752213d59EXAMPLE --options ApplianceModeSupport=enable
aws ec2 modify-transit-gateway-vpc-attachment --transit-gateway-attachment-id tgw-attach-0253EXAMPLE --options ApplianceModeSupport=enable
Combined Firewall Model
A combined model, as it indicates, is a combination of both distributed and centralized firewall models. In some use cases, it’s required to segregate the traffic of public resources (North-South) from the other two internal traffic flows: VPC to VPC and VPC to on-premises (North-South). In that case, the distributed firewall model is implemented for East-West traffic flow whereas the centralized firewall model for the North-South traffic flow.
To Sum Up
AWS Network Firewall is a good add-on to make the infrastructure cloud-native and can be implemented with different architectures using the aforementioned deployment models. AWS Network Firewall also enables the cloud watch logs which gives an insight into the traffic going through the network. Once implemented, it’s easy to manage, block, or allow various traffic with firewall policies and their set of rules.