Implementation of two-way authentication with centralized multi-region traffic management and Streamline SSL certificate management. Patch management for security and compliance and implementation of cross-region DR for high availability and enhance internal and external network security.
Problem Statement
- The customer seeks to implement a robust “two-way” authentication system, ensuring secure server-client communication while effectively managing network traffic across a multi-region infrastructure. This solution should be centrally managed to streamline operations and enhance security across all locations.
- The client faced challenges in managing domain SSL certificates and handling renewals through third-party certificate issuers. Additionally, they sought a more cost-effective solution to streamline the process and reduce expenses.
- The client was facing challenges in maintaining their Linux-based operating systems up to date with the latest security patches, which is critical for ensuring system security and compliance.
- The client required the implementation of a cross-region disaster recovery (DR) infrastructure to ensure high availability and resilience for their critical application databases and applications.
- The client sought to enhance the security of both internal and external network traffic by implementing comprehensive preventive and detective measures for all deployed AWS workloads.
Proposed Solution & Architecture
The following solutions were deployed to address the client’s challenges in a strategic, cost-effective, and efficient manner, leveraging AWS services to enhance security, optimize performance, and improve operational efficiency:
mTLS Implementation via ALB Passthrough Mode
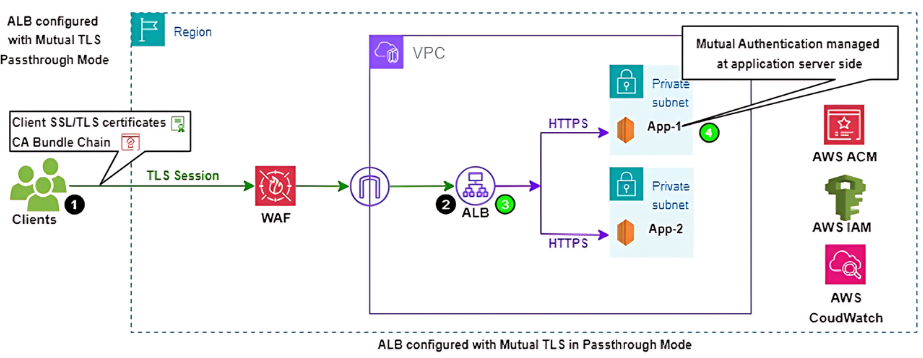
Mutual TLS (mTLS) Authentication: To address the client’s need for “two-way” authentication, we implemented AWS Application Load Balancer (ALB) with mTLS enabled in Passthrough mode. This solution provides enhanced security by ensuring both the server and the client mutually authenticate each other before establishing a connection, adding an additional layer of security at the application level.
High Availability (HA) Setup: The infrastructure was designed for high availability by deploying the ALB and application VMs in a multi-zone structure. This ensures that the services remain accessible even in the event of an availability zone failure, improving fault tolerance.
Cost Optimization: The client was previously using Network Load Balancer (NLB)in a multi-region setup, which was increasing costs. We optimized this by utilizing the ALB Passthrough mode for mTLS, which enabled us to consolidate the traffic management into a single ALB instead of deploying an NLB in each region. This change resulted in significant cost savings. Additionally, we applied AWS Compute Savings Plans based on resource utilization, further reducing the client’s monthly AWS expenses.
Automated Server Backup: Automated backups were configured for all critical servers using AWS Backup, ensuring quick restoration in the event of a system crash. This adds resilience and minimizes downtime.
Automated SSL Certificate Management
To resolve the client’s challenge in managing SSL certificates, we implemented AWS Certificate Manager (ACM) with DNS-based validation. This solution automates the issuance, renewal, and termination of SSL certificates at the ALB layer. AWS ACM is a cost-effective service (free of charge) compared to the previous third-party certificate issuer, significantly reducing costs while eliminating manual intervention for SSL renewals.
Automated Patch Management
To streamline the management of security patches on the client’s Linux-based systems, we deployed AWS Systems Manager (SSM) to automate patch management. This ensures timely application of security patches, reducing vulnerabilities and ensuring compliance with security best practices without manual overhead.
Cross-Region Disaster Recovery (DR) Infrastructure
As part of the client’s requirement for disaster recovery, we implemented a cross-region DR solution in AWS, replicating their critical application databases and infrastructure to the EU-West-1 (Ireland) region. By leveraging AWS Elastic Disaster Recovery (AWS DRS), we ensured real-time data replication with minimal Recovery Point Objective (RPO) and Recovery Time Objective (RTO). This solution provides robust DR capabilities, allowing the client to restore services quickly in the event of a disaster.
Secure Network Traffic
To secure both internal and external network traffic, we deployed comprehensive security measures, including AWS Network Firewall and AWS Web Application Firewall (WAF). AWS Network Firewall was used to protect the network perimeter by filtering and controlling traffic, while AWS WAF was used to safeguard web applications from common security threats, such as SQL injection and cross-site scripting (XSS). These preventive and detective measures ensured robust network security for all AWS workloads.
Outcomes of Project & Success Metrics
Improved Security
Cost & Operational Efficiency
High Availability and Resilience
Improved Security: Secure communication through encryption and mutual authentication. Through mTLS, automated patching, and network security services (AWS Network Firewall, WAF).
Regulatory Compliance: Met strict regulatory requirements for secure data transmission.
Cost Efficiency: Significant cost savings from ALB mTLS Passthrough mode, AWS ACM for SSL management, and Compute Savings Plans. Deployment of ALB across 10 countries hosted applications and decommissioning of NLB resulted in a reduction of service cost by nearly about 50% yearly recurring costs.
Reduced customer burden of issuing and renewing of certificates by using AWS ACM service along with SSL/TLS cost saving of approximately 30% per year
Operational Efficiency: Automation of SSL certificate renewal, patch management, and backup processes reduced manual intervention and ensured smooth operations.
High Availability and Resilience: Multi-zone HA setup and cross-region disaster recovery improved service reliability and minimized downtime.
These solutions not only addressed the client’s challenges but also optimized their AWS infrastructure for better performance, security, and cost-effectiveness
Lessons Learned
- Enhanced security with two-way authentication mechanism between client and server for secure data transmission
- mTLS introduced additional computational overhead compared to standard TLS because of both the client and server perform mutual authentication
- Used AWS ACM service to automate the SSL certificate renewal process which reduce administrative overhead and minimize the risk of human error
- Optimized performance specially for high-traffic applications
- NewRelic is used as a 3rd party solution for Monitoring.
- Cloudlytics tool is used to assess infrastructure level vulnerability.